AWS Security
Discover how to increase the security of your AWS Consultant environment with these simple tricks and best practices. Protect your cloud with expert advice on AWS security.


Introduction:
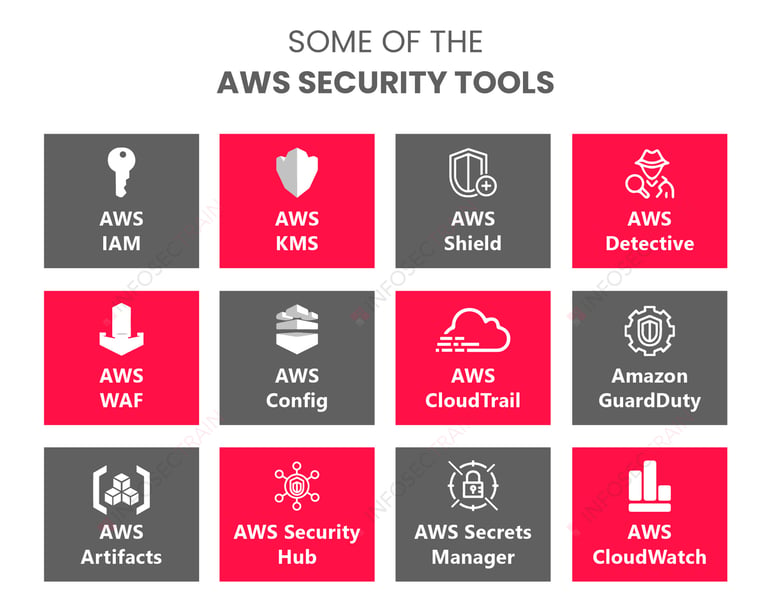
Enhancing security in your AWS environment is crucial. To keep your data and systems safe, start by using strong passwords and turning on multi-factor authentication. Control access by using IAM (Identity and Access Management) and make sure to encrypt your data. Regularly monitor activity on your systems and secure your network settings. Maintain patched and updated software, and always be prepared with backups. Review and audit your settings regularly, and make sure your team is trained on security best practices. These simple steps will greatly improve your security and help keep you safe from potential threats.
Secure Network Configuration
Securing your network setup is one of the most important actions you can take to improve security in your AWS environment. To divide and isolate your AWS resources, make use of the Virtual Private Cloud (VPC) feature. This enables you to limit access to particular resources and better manage the traffic on your network.
To further improve network security, put security groups and network access control lists (ACLs) into place. Your subnets' ACLs function as a firewall, letting you set up rules for inbound and outbound traffic to regulate its flow. On the other side, at the instance level, security groups manage the traffic going to and from your EC2 instances.
To keep your AWS resources safe, make sure to set up your network settings correctly. This keeps your resources more securely protected and lessens the possibility of unwanted access.
Strong Passwords and Multi-Factor Authentication
Creating strong passwords is a basic security measure. Make sure every user account in your Amazon environment has a strong, one-of-a-kind password. A strong password ought to have a minimum of twelve characters. A combination of capital and lowercase letters, digits, and special characters should be used.
Verify that multi-factor authentication (MFA) is activated on each user account. Through the use of a second verification code, MFA (multi-factor authentication) increases security. This code is usually generated by a mobile app or a hardware token, along with their password.
AWS environment security can be significantly reduced by using strong passwords and enabling multi-factor authentication.
Limit Access with IAM
You can control user access to AWS resources with the help of AWS Identity and Access Management (IAM). By setting up IAM policies and roles, you can give each user or group-specific permissions. This way, they can only access the resources and actions they need.
Make sure your IAM policies are current and adhere to the least privilege principle by routinely reviewing and auditing them. Remove any extra permissions and regularly change access keys to reduce the risk of unauthorized access.
You can lower the attack surface and improve the general security of your AWS system by using IAM to manage access properly.
Encrypt Your Data
Your data must be encrypted to be shielded from unwanted access. To protect your data both in transit and at rest, AWS provides several encryption alternatives, including AWS CloudHSM and AWS Key Management Service (KMS).
Using AWS KMS, you can manage your encryption keys and turn on encryption for your RDS databases, S3 buckets, and EBS volumes. Also, turn on SSL/TLS for your network traffic to keep communication between your AWS resources secure.
Encrypting your data adds extra protection. Even if your data is compromised, it will stay unreadable to anyone who isn't authorized.
Monitor Activity
It's critical to keep an eye on activity in your AWS environment in order to identify and handle any questionable or harmful activities. To track changes to your AWS resources, enable AWS Config and use AWS CloudTrail to log all API calls made in your account.
Configure alerts and notifications to notify you of any unauthorized resource changes or attempts to get access. Examine and evaluate the logs and warnings on a regular basis to spot any possible security risks.
By keeping an eye on activity in your AWS environment, you can quickly handle security issues and reduce potential risks.
Regular Updates and Patching
It’s important to regularly update and patch your software and operating systems. This helps protect against known security risks. AWS offers services like AWS Systems Manager and AWS Patch Manager that help automate updates and patches for your EC2 instances.
For your EC2 instances and other AWS resources, enable automatic upgrades and patches. Regularly review and test new patches before adding them to your production environment. This helps ensure they work well and reduces the risk of any disruptions.
Keep your software and systems updated to lower the risk of being attacked through known weaknesses. This helps make your AWS environment more secure.
Establish Backup Plans
Having backup plans is important to keep your business running smoothly and to protect your data from loss or damage. Make use of AWS services like Amazon Glacier and S3 to keep backups of your important information.
Make sure to set up automated backups regularly. Also, test the restoration process to confirm that your backups are reliable and can be quickly restored when needed. For added security against unintentional deletions or modifications, think about versioning your S3 buckets.
With strong backup plans, you can quickly recover from data loss or damage and reduce the impact of security issues.
Audit Your Settings
Make sure your AWS settings are in line with best practices and your security requirements by conducting routine audits. Examine your encryption settings, IAM policies, security group rules, and VPC setups.
Use AWS Trusted Advisor to get real-time advice and best practices for optimizing your AWS environment. It helps find any potential security issues or misconfigurations.
By regularly checking your settings, you can find and fix any security risks and keep your AWS environment secure.
Provide Team Training
Finally, teach and train your team members on AWS security best practices regularly. Ensure that everyone on your team is aware of potential security threats and why it's crucial to abide by security regulations. They should also be trained on how to respond if a security issue arises.
Think about doing simulated security drills and tabletop exercises. These helps to test your security measures and improve how well your team can respond to issues.
By offering security training to your team, you help build a culture where everyone is aware of security risks. This training allows your team members to play an active role in keeping your AWS environment safe.
To keep your AWS environment secure, it's crucial to protect your data and infrastructure from potential threats. Start by securing your network settings to prevent unauthorized access. Use strong passwords and enable Multi-Factor Authentication (MFA) for extra protection. Use Identity and Access Management (IAM) to restrict who has access to your resources. Encrypt your data to keep it safe, and regularly monitor activity to spot any unusual behaviour. Make sure to update and patch your systems frequently to address any vulnerabilities. Prepare backup strategies in case data recovery becomes necessary. Regularly review and audit your security settings, and ensure your team is trained on security best practices. By following these simple steps, you can greatly improve the security of your AWS environment and better protect your data.